In the rail fence cipher, the plaintext is written downwards on successive "rails" of an imaginary fence, starting a new column when the bottom is reached. The message is then read off in rows. For example, if we have 3 rails and a message of "This is a secret message", you would write out:
T S A C T S G H I S R M S E I S E E E A JThe last J is just a random letter to fill in the space. The secret message is then condensed and regrouped.
TSACT SGHIS RMSEI SEEEA JGURLTo decipher a message you must know the number of rails that were used to encipher it. You then break up the letters into equal groups for each rail. For example, if you are using 3 rails, you would break the secret message into 3 equal groups. Now you stack the groups on top of each other and read off the message vertically. If you get gibberish, then there are probably some extra letters tacked on the end of the message that are throwing off the grouping. Try removing one letter from the end and try again.
Rail Fence Cipher
The railfence cipher is
an easy to apply transposition cipher that jumbles up the order of the
letters of a message in a quick convenient way. It also has the security
of a key to make it a little bit harder to break.
The Rail Fence cipher
works by writing your message on alternate lines across the page, and
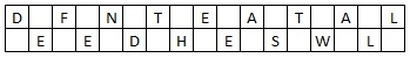
then reading off each line in turn. For example, the plaintext "defend
the east wall" is written as shown below, with all spaces removed.
The ciphertext is then read off by writing the top row first, followed by the bottom row, to get "DFNTEATALEEDHESWL".
Encryption
To encrypt a message using the Rail Fence Cipher, you have to write your message in zigzag lines across the page, and then read off each row. Firstly, you need to have a key, which for this cipher is the number of rows you are going to have. You then start writing the letters of the plaintext diagonally down to the right until you reach the number of rows specified by the key. You then bounce back up diagonally until you hit the first row again. This continues until the end of the plaintext.
To encrypt a message using the Rail Fence Cipher, you have to write your message in zigzag lines across the page, and then read off each row. Firstly, you need to have a key, which for this cipher is the number of rows you are going to have. You then start writing the letters of the plaintext diagonally down to the right until you reach the number of rows specified by the key. You then bounce back up diagonally until you hit the first row again. This continues until the end of the plaintext.
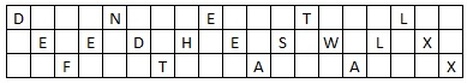
For the plaintext we used above, "defend the east wall", with a key of 3, we get the encryption process shown below.
Note that at the end of
the message we have inserted two "X"s. These are called nulls, and act
as placeholders. We do this to make the message fit neatly in to the
grid (so that there are the same number of letters on the top row, as on
the bottom row. Although not necessary, it makes the decryption process
a lot easier if the message has this layout.
The ciphertext is read off row by row to get "DNETLEEDHESWLXFTAAX".
Decryption
The decryption process for the Rail Fence Cipher involves reconstructing the diagonal grid used to encrypt the message. We start writing the message, but leaving a dash in place of the spaces yet to be occupied. Gradually, you can replace all the dashes with the corresponding letters, and read off the plaintext from the table.
The decryption process for the Rail Fence Cipher involves reconstructing the diagonal grid used to encrypt the message. We start writing the message, but leaving a dash in place of the spaces yet to be occupied. Gradually, you can replace all the dashes with the corresponding letters, and read off the plaintext from the table.
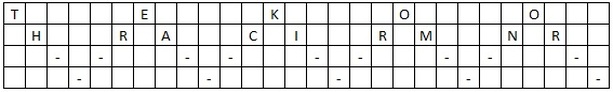
We start by making a
grid with as many rows as the key is, and as many columns as the length
of the ciphertext. We then place the first letter in the top left
square, and dashes diagonally downwards where the letters will be. When
we get back to the top row, we place the next letter in the ciphertext.
Continue like this across the row, and start the next row when you reach
the end.
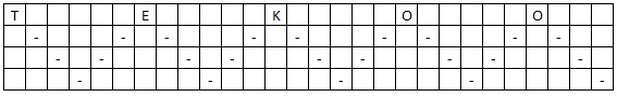
For example, if you
receive the ciphertext "TEKOOHRACIRMNREATANFTETYTGHH", encrypted with a
key of 4, you start by placing the "T" in the first square. You then
dash the diagonal down spaces until you get back to the top row, and
place the "E" here. Continuing to fill the top row you get the pattern
below.
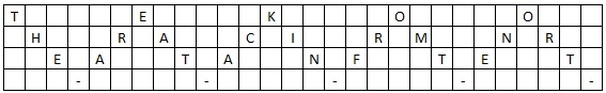
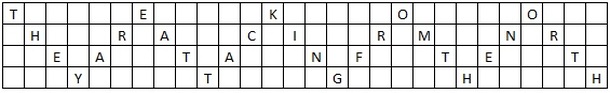
Continuing this row-by-row, we get the successive stages shown below.
From this we can now read the plaintext off following the diagonals to get "they are attacking from the north".
Discussion
The Rail Fence Cipher is a very easy to apply transposition cipher. However, it is not particularly secure, since there are a limited number of usable keys, especially for short messages (for there to be enough movement of letters, the length of the message needs to be at lease twice the key, but preferably 3 times the key). You could process these quite quickly by hand, and even more quickly with a computer.
The Rail Fence Cipher is a very easy to apply transposition cipher. However, it is not particularly secure, since there are a limited number of usable keys, especially for short messages (for there to be enough movement of letters, the length of the message needs to be at lease twice the key, but preferably 3 times the key). You could process these quite quickly by hand, and even more quickly with a computer.
The use of nulls can
also have a detrimental effect on the security of the cipher, as an
interceptor can use them to identify where the end of the line is, and
so have a sensible guess at the key. This can be averted by using a more
common letter, such as "E", to fill the null spaces, as it will still
be clear to the recipient that these are not part of the message as they
will appear at the end of the plaintext. The Rail Fence Cipher can also
be utilised without the use of nulls.
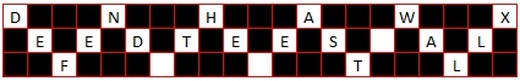
One way to also make the
encryption a little bit more secure, is to keep the spaces as
characters, and include them in the encryption table. They are treated
in exactly the same way as any other letter. For example, using the
plaintext "defend the east wall" with a key of 3 again, but this time
including spaces we get the table below.
So the ciphertext would read "DNHAWXEEDTEES ALF TL".







.jpg)
.jpg)


.jpg)




0 comments:
Post a Comment
Note: Only a member of this blog may post a comment.